How Truly Random Numbers Are Generated
As of 2026, true random number generation is achieved b […]
Resumo rápido
- As of 2026, true random number generation is achieved b
- As of 2026, true random number generation is achieved by harvesting physical entropy from non-deterministic sources like atmospheric noise, thermal fluctuations, or quantum decay.
- The Mechanics of Randomness: How Truly Random Numbers Are Generated
Processo editorial
Revisado por SectoJoy e publicado em 7 de maio de 2026. Atualizamos este artigo quando os detalhes do produto, exemplos ou guia da ferramenta mudam. Última atualização: 7 de maio de 2026.
SectoJoy
Sou um desenvolvedor independente que cria aplicativos iOS e web, focado em produtos SaaS práticos. Tenho especialização em SEO com IA, explorando constantemente como tecnologias inteligentes podem impulsionar crescimento sustentável e eficiência.
As of 2026, true random number generation is achieved by harvesting physical entropy from non-deterministic sources like atmospheric noise, thermal fluctuations, or quantum decay. Unlike algorithm-based generators, these hardware-driven systems measure chaotic environmental variables to ensure digital sequences remain mathematically unpredictable and pattern-free for high-stakes security.
The Mechanics of Randomness: How Truly Random Numbers Are Generated
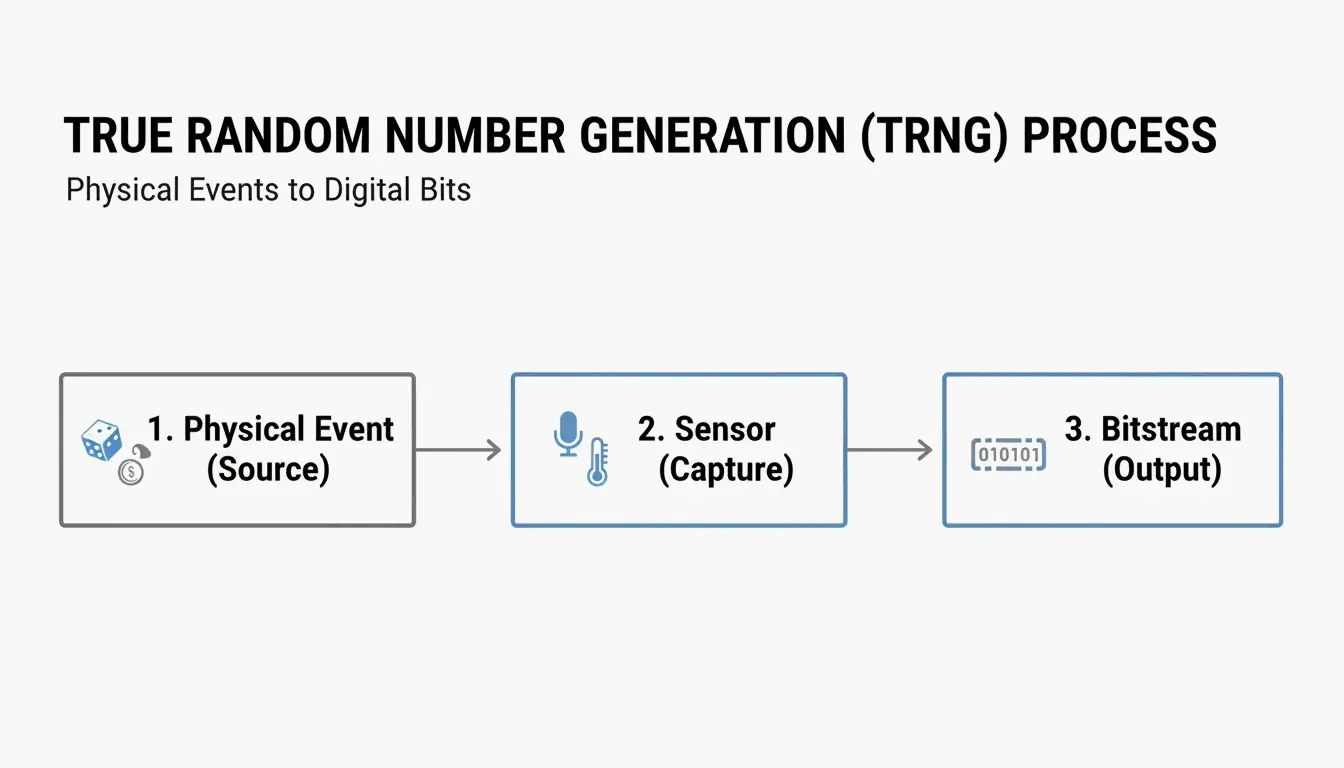
To understand how truly random numbers are generated, you first have to look at the difference between mathematical patterns and physical chaos. A True Random Number Generator (TRNG), also called a Hardware Random Number Generator (HRNG), doesn’t follow a pre-set equation. Instead, it acts as a bridge between the unpredictable physical world and the rigid logic of digital systems.
The process works by capturing an external Entropy Source—a physical event that is basically impossible to map or predict—and turning its analog signals into a stream of binary bits. Without this outside “noise,” a computer is stuck in what John von Neumann famously described in 1951: “Anyone who considers arithmetical methods of producing random digits is, of course, in a state of sin.”
The Hardware Layer: How Your Device Captures Chaos
Modern devices pick up on randomness through specialized sensors that detect tiny environmental shifts. According to Wikipedia, common physical sources include:
- Thermal Noise: Tiny voltage zig-zags caused by the heat-driven movement of electrons in a circuit.
- Atmospheric Noise: Radio static created by natural events like lightning strikes.
- Quantum Phenomena: Measuring the radioactive decay of an isotope or vacuum fluctuations—events that are inherently unpredictable by the laws of physics.
TRNG vs. PRNG: Understanding the Deterministic Divide
The big split in random number generation is between physical entropy and algorithmic logic. A Pseudorandom Number Generator (PRNG) uses a Seed Value—a starting point fed into a mathematical formula to churn out a long string of numbers. While these numbers look random, they are actually deterministic. If someone knows the seed and the math behind it, they can predict every single number that follows.
This weakness has caused real trouble. One famous example is the Hot Lotto Fraud Scandal. An insider rigged a $16.5 million jackpot by installing malware that forced the PRNG to use a predictable seed during maintenance.
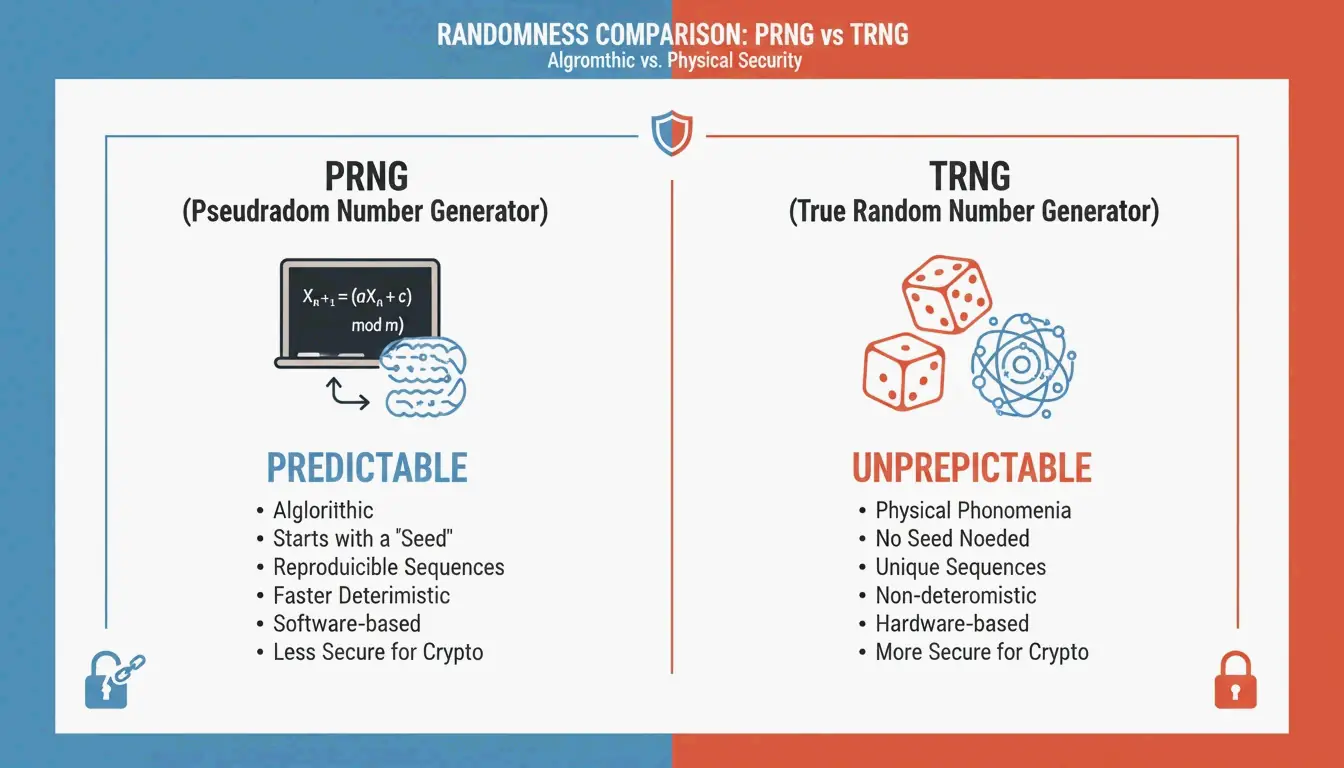
To fix this, most modern systems use a hybrid called a Cryptographically Secure Pseudorandom Number Generator (CSPRNG). These systems pull a small amount of “true” entropy from hardware to seed a fast algorithm. This gives you the best of both worlds: the unpredictability of a TRNG with the high speed of a PRNG.
When to Use PRNG: Efficiency and the Monte Carlo Method
Even though they are predictable, PRNGs are actually better for tasks where speed and the ability to repeat a test matter. In Monte Carlo Method simulations, scientists need to run the same sequence of numbers multiple times to check for bugs or verify data. Because you can reuse the same seed, the simulation stays consistent—something a “blocking” TRNG just can’t do.
Modern Implementation: TRNGs in 2026 Consumer Hardware
By 2026, hardware entropy has moved from high-end servers straight into our pockets. Modern smartphone chips, like the Apple A-series or Google Tensor, now have dedicated TRNGs built into their Secure Enclaves.
These enclaves pick up thermal noise directly from the processor to create encryption keys. This keeps your most sensitive data, like FaceID info or digital wallet keys, hidden away from the main operating system. For high-level enterprise security, the focus is shifting toward Quantum Randomness. Systems like those at the Australian National University (ANU) generate numbers from quantum vacuum fluctuations, creating a level of randomness that even future brute-force computers likely won’t be able to crack.
From Raw Noise to Pure Data: The Role of Whitening and Post-Processing
Raw entropy from the environment is rarely perfect right off the bat. Physical sources often have a “bias”—for example, a thermal sensor might spit out slightly more “1s” than “0s” because of a temperature change. To fix this, the data goes through a process called “Whitening.”
Whitening runs the biased bits through a cryptographic function (like an XOR operation) to smooth out patterns and make sure the distribution is even. Modern tech has to follow strict global rules, specifically NIST SP 800-90A, which sets the standard for how these generators must be built to be safe for government and industrial use.
Coding for Security: secrets vs random in Modern Languages
For developers, picking the right library is a major security choice. Most standard libraries, like Python’s random module, use the Mersenne Twister. It’s fast, but it’s a PRNG and isn’t safe for security. Instead, developers should use the secrets module in Python or crypto.getRandomValues() in JavaScript. These are built to talk to the OS-level entropy pool (like /dev/urandom), making sure the output is actually secure.
A Brief History of Harvesting Chaos
The hunt for randomness started long before computers. Early methods were as simple as rolling dice or flipping coins. A big milestone was L.H.C. Tippett’s 1927 table, which listed 41,600 digits pulled manually from census records. Later, in 1955, the RAND Corporation published A Million Random Digits, using an electronic pulse machine to give statisticians a reliable resource.
But the history of RNG also has a darker side involving intentional tampering. The case of Dual_EC_DRBG, a NIST-certified generator, is a famous warning. Reports in 2013 confirmed the NSA had put a backdoor into the algorithm, allowing them to figure out the generator’s state and crack secure SSL connections. This discovery pushed the industry to start mixing hardware entropy with several different sources so that no single point of failure could be exploited.
Conclusion
Truly random numbers are the foundation of digital trust. They require physical hardware to bridge the gap between predictable code and the messy, chaotic reality of the physical world. Whether it’s thermal noise in your phone or quantum shifts in a server room, moving from “pseudo-randomness” to true physical entropy is a must for security in 2026. For developers, the rule is simple: use secure libraries like Python’s secrets instead of basic math functions. For companies, using hardware-verified TRNGs for encryption is no longer just a “nice to have”—it’s a basic requirement for keeping data safe.
FAQ
Is my computer’s internal clock a source of true randomness?
No, the internal clock is predictable. While it’s often used as a “seed” for PRNGs because it’s always changing, a hacker who knows roughly when a number was generated can narrow down the possibilities. True randomness requires timing non-deterministic events, like the gap between keystrokes or atmospheric noise, followed by statistical whitening.
Can a human being generate a truly random sequence of numbers?
Humans are actually pretty bad at being random because of how our brains work. We tend to avoid clusters (like “1, 1, 1”) even though those happen often in real random sets. We also tend to switch back and forth between options too much. Statistical tests can easily spot these human patterns, which is why human input is okay for “seeding” but not enough for high-security tasks.
What are the common statistical tests used to verify if a sequence is truly random?
The NIST Statistical Test Suite (STS) is the gold standard for checking randomness. Other common frameworks include the “Dieharder” tests and the AIS 31 standard. These tests hunt for oddities like repeating patterns or long runs of the same bit that would suggest the sequence is biased or predictable rather than truly random.
Perguntas frequentes
Is my computer’s internal clock a source of true randomness?
No, the internal clock is predictable. While it’s often used as a “seed” for PRNGs because it’s always changing, a hacker who knows roughly when a number was generated can narrow down the possibilities. True randomness requires timing non-deterministic events, like the gap between keystrokes or atmospheric noise, followed by statistical whitening.
Can a human being generate a truly random sequence of numbers?
Humans are actually pretty bad at being random because of how our brains work. We tend to avoid clusters (like “1, 1, 1”) even though those happen often in real random sets. We also tend to switch back and forth between options too much. Statistical tests can easily spot these human patterns, which is why human input is okay for “seeding” but not enough for high-security tasks.
What are the common statistical tests used to verify if a sequence is truly random?
The NIST Statistical Test Suite (STS) is the gold standard for checking randomness. Other common frameworks include the “Dieharder” tests and the AIS 31 standard. These tests hunt for oddities like repeating patterns or long runs of the same bit that would suggest the sequence is biased or predictable rather than truly random.
Artigos Relacionados
Random Phone Number Generator: A Guide to Testing and SMS Verification

SME Inventory Management: How to Build a Low Cost Fixed Asset Barcode System

How to Pick a Raffle Winner Fairly: The Ultimate Guide to Random Legal Draws
